How did the LuBian mining pool lose nearly 130,000 bitcoins to theft in 2020?
Using a predictable pseudo-random number generator led to private keys being compromised, and the "culprit" may be the US government.
The use of easily predictable pseudo-random number generators led to private key collisions, and the "culprit" may be the U.S. government.
Original Title: "Technical Traceability Analysis Report on the LuBian Mining Pool Hacking Incident and Massive Bitcoin Theft"
Author: Wukong
On December 29, 2020, the LuBian mining pool suffered a major hacking incident, with a total of 127,272.06953176 bitcoins (worth about $3.5 billion at the time, now valued at $15 billion) stolen by the attacker. The holder of this massive amount of bitcoin was Chen Zhi, chairman of Cambodia's Prince Group. After the hacking incident, Chen Zhi and his Prince Group repeatedly posted messages on the blockchain in early 2021 and July 2022, appealing to the hacker to return the stolen bitcoins and expressing willingness to pay a ransom, but received no response. Strangely, after the theft, these bitcoins remained dormant in the attacker's controlled bitcoin wallet address for as long as four years, with almost no movement, which is clearly inconsistent with the usual behavior of hackers eager to cash out for profit. Instead, it resembles a precise operation orchestrated by a "state-level hacker organization." It was not until June 2024 that the stolen bitcoins were transferred again to new bitcoin wallet addresses, where they remain untouched to this day.
On October 14, 2025, the U.S. Department of Justice announced criminal charges against Chen Zhi and stated that it had confiscated 127,000 bitcoins from Chen Zhi and his Prince Group. Various pieces of evidence indicate that the massive amount of bitcoin confiscated by the U.S. government from Chen Zhi and his Prince Group was in fact the same batch of bitcoins stolen from the LuBian mining pool by hackers using technical means as early as 2020. In other words, the U.S. government may have already stolen Chen Zhi's 127,000 bitcoins through hacking techniques as early as 2020—this is a typical "black eats black" incident orchestrated by a state-level hacker organization. This report, from a technical perspective, conducts a technical traceability analysis, delves into the key technical details of the incident, focuses on the ins and outs of the bitcoin theft, reconstructs the complete attack timeline, and evaluates the security mechanisms of bitcoin, hoping to provide valuable security insights for the cryptocurrency industry and its users.
Incident Background
LuBian mining pool was established in early 2020 and quickly rose as a bitcoin mining pool, with China and Iran as its main operating bases. In December 2020, LuBian mining pool suffered a large-scale hacking attack, resulting in the theft of over 90% of its bitcoin holdings. The total amount stolen was 127,272.06953176 BTC, which closely matches the 127,271 BTC mentioned in the U.S. Department of Justice indictment.
The operating model of LuBian mining pool included centralized storage and distribution of mining rewards. The bitcoins in the pool addresses were not stored in regulated centralized exchanges, but in non-custodial wallets. Technically, non-custodial wallets (also known as cold wallets or hardware wallets) are considered the ultimate safe haven for crypto assets. Unlike exchange accounts that can be frozen by a court order, they are more like a bank vault that belongs solely to the holder, with the key (private key) only in the holder's hands.
As a cryptocurrency, bitcoin uses on-chain addresses to identify the ownership and flow of bitcoin assets. Possession of the private key to an on-chain address gives full control over the bitcoins in that address. According to reports from on-chain analysis institutions, the massive amount of bitcoin controlled by the U.S. government and belonging to Chen Zhi highly overlaps with the LuBian mining pool hacking incident. On-chain data records show that on December 29, 2020 (UTC+8), LuBian's core bitcoin wallet address experienced abnormal transfers totaling 127,272.06953176 BTC, which closely matches the 127,271 BTC mentioned in the U.S. Department of Justice indictment. After being abnormally transferred, these stolen bitcoins remained dormant until June 2024. Between June 22 and July 23, 2024 (UTC+8), the stolen bitcoins were again transferred to new on-chain addresses, where they remain untouched. The well-known U.S. blockchain tracking platform ARKHAM has labeled these final addresses as being held by the U.S. government. So far, the U.S. government has not disclosed in the indictment how it obtained the private keys to Chen Zhi's massive bitcoin on-chain addresses.
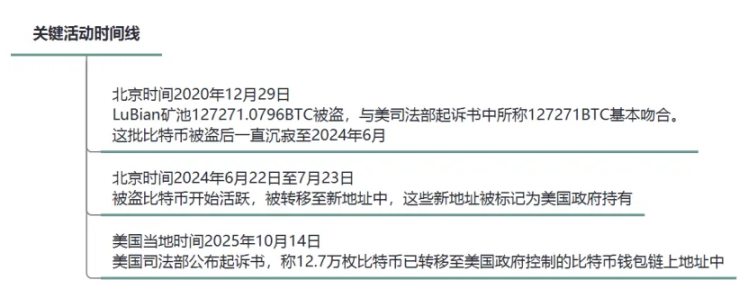
Figure 1: Key Activity Timeline
Attack Chain Analysis
It is well known that in the blockchain world, randomness is the cornerstone of cryptographic security. Bitcoin uses asymmetric encryption technology, and the bitcoin private key is a string of 256-bit binary random numbers, with a theoretical brute-force count of 2^256, which is virtually impossible. However, if this 256-bit binary private key is not completely random—for example, if 224 bits follow a predictable pattern and only 32 bits are random—then the private key strength is greatly reduced, and it would only take 2^32 (about 4.29 billion) attempts to brute-force it. For example, in September 2022, the British crypto market maker Wintermute lost $160 million due to a similar pseudo-random number vulnerability.
In August 2023, the overseas security research team MilkSad first disclosed that a third-party key generation tool had a pseudo-random number generator (PRNG) vulnerability and successfully obtained a CVE number (CVE-2023-39910). In their published research report, they mentioned that the LuBian bitcoin mining pool had a similar vulnerability, and among the LuBian bitcoin mining pool addresses attacked by hackers, all 25 bitcoin addresses listed in the U.S. Department of Justice indictment were included.
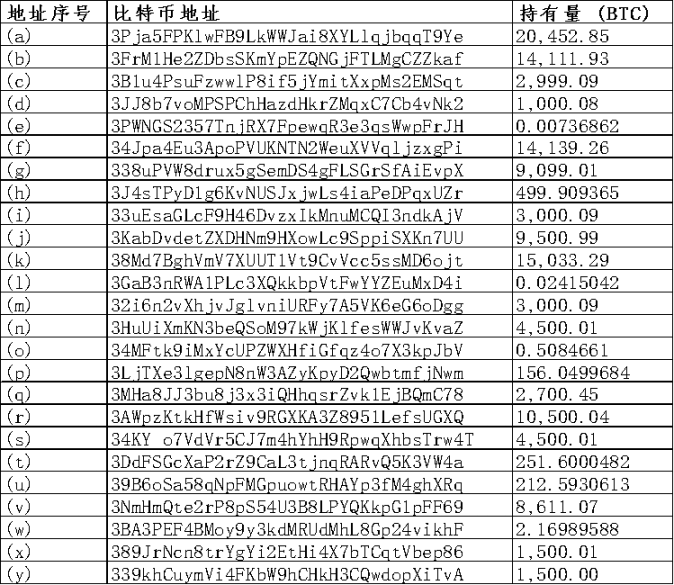
Figure 2: List of 25 Bitcoin Wallet Addresses in the U.S. Department of Justice Indictment
As a non-custodial wallet system, the LuBian bitcoin mining pool relied on a custom private key generation algorithm to manage funds, but the private key generation did not use the recommended 256-bit binary random number standard. Instead, it relied on a 32-bit binary random number. This algorithm had a fatal flaw: it only relied on a timestamp or weak input as the seed for the "pseudo-random generator" Mersenne Twister (MT19937-32). A pseudo-random number generator (PRNG) with only 4 bytes of randomness can be efficiently brute-forced with modern computing. Mathematically, the probability of cracking is 1/2^32. For example, if an attack script tests 10^6 keys per second, the cracking time is about 4,200 seconds (just about 1.17 hours). In practice, optimized tools like Hashcat or custom scripts can further accelerate the process. The attacker exploited this vulnerability to steal the massive amount of bitcoin from the LuBian mining pool.
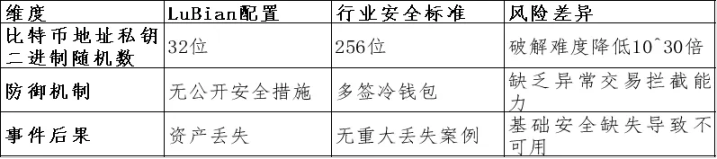
Figure 3: Comparison Table of LuBian Mining Pool and Industry Security Standards Defects
Through technical traceability, the complete timeline and related details of the LuBian mining pool hacking incident are as follows:
Theft Phase: December 29, 2020 (UTC+8)
Event: The hacker exploited the pseudo-random number vulnerability in the LuBian mining pool bitcoin wallet private key generation to brute-force over 5,000 weak random wallet addresses (wallet type: P2WPKH-nested-in-P2SH, prefix 3). In about 2 hours, about 127,272.06953176 BTC (worth about $3.5 billion at the time) was drained from these wallet addresses, leaving less than 200 BTC. All suspicious transactions shared the same transaction fee, indicating that the attack was executed by an automated batch transfer script.
Sender: LuBian mining pool weak random bitcoin wallet address group (controlled by LuBian mining operation entity, under Chen Zhi's Prince Group);
Recipient: Attacker-controlled bitcoin wallet address group (addresses not disclosed);
Transfer Path: Weak wallet address group → Attacker wallet address group;
Correlation Analysis: The total amount stolen was 127,272.06953176 BTC, which closely matches the 127,271 BTC mentioned in the U.S. Department of Justice indictment.
Dormancy Phase: December 30, 2020 to June 22, 2024 (UTC+8)
Event: After being stolen via the pseudo-random number vulnerability in 2020, these bitcoins were stored in attacker-controlled bitcoin wallet addresses for as long as four years, remaining dormant, with only a negligible amount of dust transactions possibly used for testing.
Correlation Analysis: Until the U.S. government fully took over on June 22, 2024, these bitcoins were almost untouched, which is clearly inconsistent with the usual behavior of hackers eager to cash out for profit. Instead, it resembles a precise operation orchestrated by a state-level hacker organization.
Recovery Attempt Phase: Early 2021, July 4 and 26, 2022 (UTC+8)
Event: After the theft, during the dormancy period, in early 2021, the LuBian mining pool sent over 1,500 messages via Bitcoin's OP_RETURN function (spending about 1.4 BTC in fees), embedding them in the blockchain data area, pleading with the hacker to return the funds. Example message: "Please return our funds, we'll pay a reward." On July 4 and 26, 2022, the LuBian mining pool again sent messages via Bitcoin's OP_RETURN function, such as: "MSG from LB. To the whitehat who is saving our asset, you can contact us through 1228btc@gmail.com to discuss the return of asset and your reward."
Sender: LuBian weak random bitcoin wallet address (controlled by LuBian mining operation entity, under Chen Zhi's Prince Group);
Recipient: Attacker-controlled bitcoin wallet address group;
Transfer Path: Weak wallet address group → Attacker wallet address group; small transactions embedded in OP_RETURN);
Correlation Analysis: After the theft, these messages confirm that the LuBian mining pool, as the sender, repeatedly tried to contact the "third-party hacker," requesting the return of assets and negotiating ransom matters.
Activation and Transfer Phase: June 22 to July 23, 2024 (UTC+8)
Event: Bitcoins in the attacker-controlled bitcoin wallet address group were activated from dormancy and transferred to final bitcoin wallet addresses. The final wallet addresses were labeled as held by the U.S. government by the well-known blockchain tracking platform ARKHAM.
Sender: Attacker-controlled bitcoin wallet address group;
Recipient: Newly consolidated final wallet address group (not disclosed, but confirmed to be U.S. government-controlled wallet address group)
Transfer Path: Attacker-controlled bitcoin wallet address group → U.S. government-controlled wallet address group;
Correlation Analysis: This massive amount of stolen bitcoin, after being dormant for four years with almost no movement, was ultimately controlled by the U.S. government.
Announcement and Seizure Phase: October 14, 2025 (U.S. local time)
Event: The U.S. Department of Justice issued an announcement, stating that it had filed charges against Chen Zhi and "seized" his 127,000 bitcoins.
At the same time, through the blockchain's public mechanism, all bitcoin transaction records are publicly traceable. Based on this, this report traces the source of the massive amount of bitcoin stolen from LuBian's weak random bitcoin wallet addresses (controlled by LuBian mining operation entity, possibly under Chen Zhi's Prince Group). The total number of stolen bitcoins is 127,272.06953176, sourced from: about 17,800 from independent "mining," about 2,300 from mining pool wage income, and about 107,100 from exchanges and other channels. Preliminary results show discrepancies with the U.S. Department of Justice indictment, which claims all were from illegal income.
Technical Details of the Vulnerability
Bitcoin Wallet Address Private Key Generation
The core of the LuBian mining pool vulnerability lies in its private key generator, which used a flaw similar to the "MilkSad" defect in Libbitcoin Explorer. Specifically, the system used the Mersenne Twister (MT19937-32) pseudo-random number generator, initialized with only a 32-bit seed, resulting in an effective entropy of only 32 bits. This PRNG is non-cryptographic, easily predictable, and reversible. Attackers can enumerate all possible 32-bit seeds (0 to 2^32-1), generate the corresponding private keys, and check if they match the public key hash of known wallet addresses.
In the bitcoin ecosystem, the private key generation process is usually: random seed → SHA-256 hash → ECDSA private key.
The implementation of LuBian mining pool's base library may have been based on custom code or open-source libraries (such as Libbitcoin), but ignored entropy security. Similar to the MilkSad vulnerability, the "bx seed" command in Libbitcoin Explorer also uses the MT19937-32 random number generator, relying only on a timestamp or weak input as the seed, making the private key vulnerable to brute-force attacks. In the LuBian attack, more than 5,000 wallets were affected, indicating a systemic vulnerability, possibly due to code reuse during batch wallet generation.
Simulated Attack Process
- Identify target wallet addresses (by monitoring LuBian mining pool activities on-chain);
- Enumerate 32-bit seeds: for seed in 0 to 4294967295;
- Generate private key: private_key = SHA256(seed);
- Derive public key and address: use ECDSA SECP256k1 curve calculation;
- Match: If the derived address matches the target, use the private key to sign a transaction and steal the funds;
Comparison with Similar Vulnerabilities: This vulnerability is similar to Trust Wallet's 32-bit entropy flaw, which once led to large-scale bitcoin wallet address cracking; the "MilkSad" vulnerability in Libbitcoin Explorer also exposed private keys due to low entropy. These cases all stem from legacy issues in early codebases that did not use the BIP-39 standard (12-24 word seed phrases, providing high entropy). LuBian mining pool may have used a custom algorithm intended to simplify management but neglected security.
Lack of Defense: LuBian mining pool did not implement multi-signature (multisig), hardware wallets, or hierarchical deterministic wallets (HD wallets), all of which could enhance security. On-chain data shows that the attack covered multiple wallets, indicating a systemic vulnerability rather than a single point of failure.
On-chain Evidence and Recovery Attempts
OP_RETURN Messages: LuBian mining pool sent over 1,500 messages via Bitcoin's OP_RETURN function, spending 1.4 BTC, pleading with the attacker to return the funds. These messages are embedded in the blockchain, proving they were actions of the real owner, not forgeries. Example messages include "Please return the funds" or similar pleas, distributed across multiple transactions.
Attack Correlation Analysis
On October 14, 2025 (U.S. local time), the U.S. Department of Justice's criminal indictment against Chen Zhi (case number 1:25-cr-00416) listed 25 bitcoin wallet addresses, which held about 127,271 BTC, with a total value of about $15 billion, and have been seized. Through blockchain analysis and review of official documents, these addresses are highly related to the LuBian mining pool hacking incident:
Direct Correlation: Blockchain analysis shows that the 25 addresses in the U.S. Department of Justice indictment are the final holding addresses of the bitcoins stolen in the 2020 LuBian mining pool attack. Elliptic's report points out that these bitcoins were "stolen" from LuBian mining pool's mining operations in 2020. Arkham Intelligence confirms that the funds seized by the U.S. Department of Justice directly originated from the LuBian mining pool theft incident.
Indictment Evidence Correlation: Although the U.S. Department of Justice indictment does not directly name the "LuBian hack," it mentions that the funds originated from "stolen attacks on bitcoin mining operations in Iran and China," which is consistent with the on-chain analysis by Elliptic and Arkham Intelligence.
Attack Behavior Correlation: In terms of attack methods, after being technically stolen in 2020, the massive amount of bitcoin from the LuBian mining pool remained dormant for four years, with only a negligible amount of dust transactions, and was almost untouched until it was fully taken over by the U.S. government in 2024. This is inconsistent with the usual behavior of hackers eager to cash out for profit, and more like a precise operation orchestrated by a state-level hacker organization. Analysis suggests that the U.S. government may have already controlled these bitcoins as early as December 2020.
Impact and Recommendations
The 2020 LuBian mining pool hacking incident had far-reaching consequences, leading to the actual dissolution of the mining pool, with losses amounting to over 90% of its total assets at the time. The value of the stolen bitcoins has now risen to $15 billion, highlighting the risk amplification caused by price volatility.
The LuBian mining pool incident exposed systemic risks in random number generation within the cryptocurrency toolchain. To prevent similar vulnerabilities, the blockchain industry should use cryptographically secure pseudo-random number generators (CSPRNG); implement multi-layered defenses, including multi-signature (multisig), cold storage, and regular audits; avoid custom private key generation algorithms; and mining pools should integrate real-time on-chain monitoring and abnormal transfer alert systems. Ordinary users should avoid using unverified key generation modules from the open-source community. This incident also reminds us that even with blockchain's high transparency, weak security foundations can still lead to catastrophic consequences. It also highlights the importance of cybersecurity in the future development of the digital economy and digital currencies.
Disclaimer: The content of this article solely reflects the author's opinion and does not represent the platform in any capacity. This article is not intended to serve as a reference for making investment decisions.
You may also like
Interpretation of b402: From AI Payment Protocol to Service Marketplace, BNBChain's Infrastructure Ambitions
b402 is not just an alternative to x402 on BSC; it could be the starting point for a much bigger opportunity.
Shutdown Leaves Fed Without Key Data as Job Weakness Deepens

Institutional Investors Turn Their Backs on Bitcoin and Ethereum

Litecoin LTC Price Prediction 2025, 2026 – 2030: Can Litecoin Reach $1000 Dollars?

